Washington – U.S. cybersecurity analysts are investigating a series of anomalies affecting major meal delivery platforms after one leading delivery company confirmed it recently experienced a cyberattack that disrupted parts of its ordering and logistics systems before being contained and resolved.
The company, which officials declined to name publicly due to the ongoing investigation, said the incident did not result in a prolonged outage but did temporarily interfere with order accuracy, delivery routing, and estimated arrival times. Service has since stabilized, though cybersecurity experts say the incident may be part of a broader pattern of activity linked to Iran-aligned cyber actors.
“This is about creating friction in everyday life,” said Dr. Melissa Harding, director of threat intelligence at ShieldPoint Cyber. “You are not shutting down infrastructure. You are undermining trust in systems people rely on constantly.”
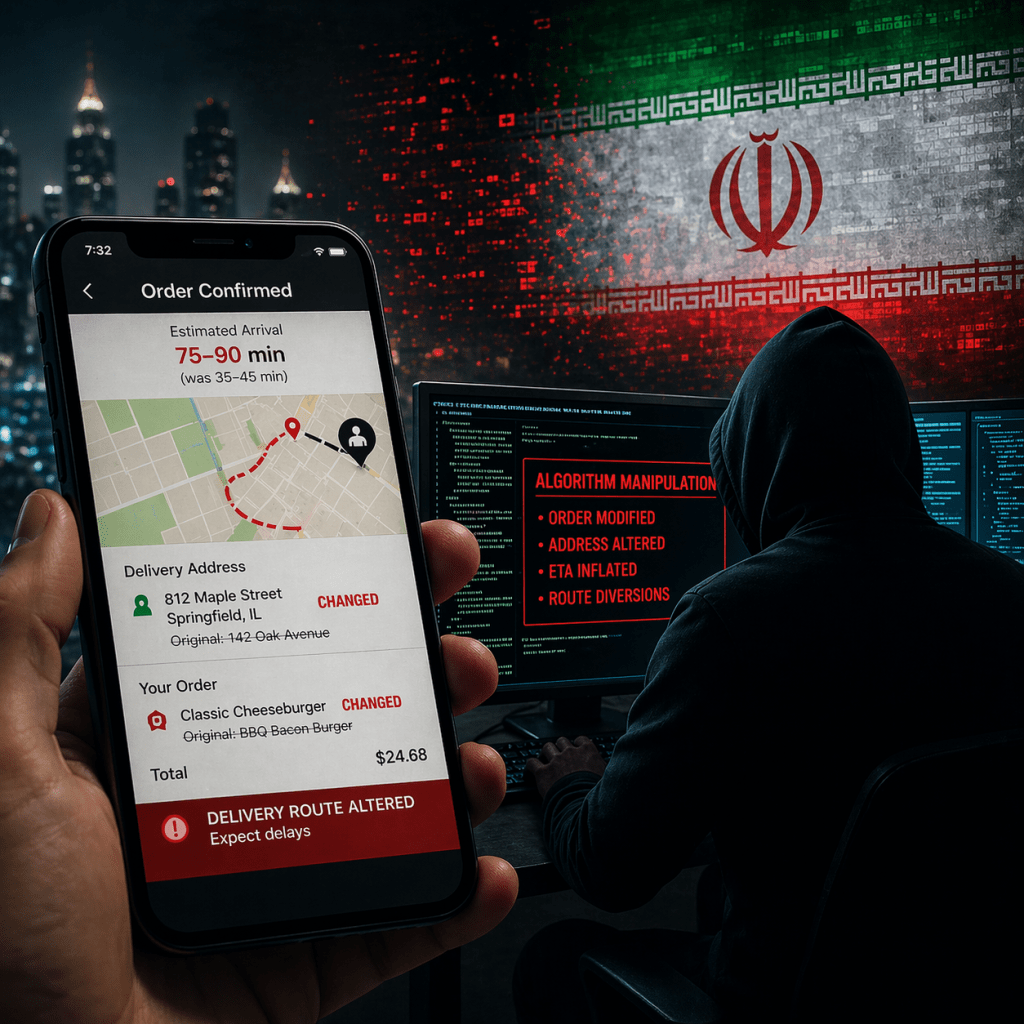
According to analysts tracking the activity, the tactics observed in the confirmed incident focused on manipulating the algorithmic backbone that powers delivery platforms. Rather than stealing data or locking systems, the attackers appear to have altered how the system processed and executed orders.
During the disruption, some users reported orders changing after they were placed, delivery addresses being mismatched, estimated wait times fluctuating unpredictably, and drivers being routed through unusually congested or inefficient paths. While the company has not publicly detailed the full scope of the attack, officials familiar with the response say the issues were traced to unauthorized interference with backend logic systems.
“They are not breaking the system outright,” said Ethan Cole, chief security analyst at Veritas Cyber Defense. “They are corrupting the logic inside it. That is what makes it so difficult to detect and potentially effective if scaled.”
Threat intelligence reports suggest that several Iran-aligned cyber collectives may be involved, often operating through loosely affiliated proxy networks. Groups identified in ongoing monitoring include the Quds Signal Directorate, the Crimson Sand Collective, and the Basalt Fox Unit, which analysts describe as part of a broader ecosystem of actors aligned with Iranian strategic interests.
“These groups do not need to take credit publicly,” said Liam O’Donnell, a former cyber operations officer now working in the private sector. “Their success is measured in confusion, not headlines.”
The focus on meal delivery apps reflects a shift toward highly visible, high-frequency services embedded in daily life. These platforms rely on real-time coordination between customers, restaurants, mapping systems, and independent drivers. Even minor disruptions can ripple outward quickly.
“You are dealing with high volume, tight timing, and constant algorithmic decision making,” said Rachel Kim, a senior fellow specializing in cyber conflict. “If you introduce even small distortions, you can create outsized effects very quickly.”
Beyond the technical mechanics, analysts say the broader impact may be psychological and behavioral. When routine services begin to behave unpredictably, even briefly, it can alter how people interact with technology and with each other.
“What we are seeing is the compounding erosion of trust,” Harding said. “People start second guessing the app, the driver, the restaurant. That uncertainty adds friction to something that is supposed to be seamless.”
Users affected during the incident described frustration that extended beyond a single delayed meal. Repeated errors over a short period created confusion and, in some cases, led customers to abandon orders altogether.
“It sounds minor until it keeps happening,” Cole said. “Then it becomes part of your daily experience. You stop trusting the timing, you stop trusting the outcome, and eventually you start questioning the platform as a whole.”
For delivery drivers and restaurants, the disruption had compounding effects even within a limited window. Drivers lost time navigating to incorrect destinations or sitting in unexpected traffic patterns. Restaurants faced increased complaints and refunds despite having no control over the underlying issue.
“There is a ripple effect,” O’Donnell said. “One manipulated data point can impact multiple people across the chain. Multiply that across a city, and you create widespread inefficiency and frustration.”
Experts say this type of activity aligns with a broader cyber strategy focused on persistent, low-level disruption that blurs the line between technical malfunction and deliberate interference.
“If users cannot tell whether a problem is a glitch or something more intentional, that ambiguity works in the attacker’s favor,” Kim said. “It creates a background level of doubt.”
Cybersecurity officials note that Iran has spent years developing cyber capabilities and cultivating affiliated hacker networks, enabling operations that can be carried out with varying degrees of attribution. Analysts caution that if the confirmed incident is part of a coordinated effort, it may represent an early-stage test rather than a fully scaled campaign.
“There are likely more attempts happening than are visible,” one analyst said, noting that irregularities in complex systems are often dismissed as routine bugs.
For now, officials emphasize that the affected company has recovered and implemented additional safeguards, while other firms across the delivery sector have increased monitoring for unusual behavior. The broader concern, experts say, is not just the disruption itself but what it signals about future tactics.
“When your dinner does not show up and it keeps happening, you start to question the reliability of the system,” Harding said. “That erosion of trust is the objective.”
As Cole put it, the implications extend beyond any single platform.
“You do not need to take down a system to make an impact,” he said. “You just need to make it stop working the way people expect.”